How does Ekkiden cultivate the entrepreneurial spirit of its teams?
Geoffrey (CEO) 'In concrete terms, entrepreneurship means going to the end of yourself and reach fulfillment thanks to a project. In a more...
Dive deeper into cybersecurity and learn about CTI to discover if you have what it takes to build the future of the digital landscape. CTI goes further than the usual barriers and adds a proactive approach to cybersecurity, one that will also determine some of the necessary skills to work in this discipline.
Image by © cottonbro studio via Pexels
Published in Our tips

In the digital era in which we live, our whole life is encrypted in the form of data. Therefore, safeguarding said data has never been so important. Companies and individuals alike can see their information and its safety compromised if an attack or a breach happens, this being the reason why CTI has gained the importance it has gained.
CTI or Cyber Threat Intelligence is a discipline, encompassed within cybersecurity, oriented towards analysing information and insights gathered to detect cyber threats and defend from current or future ones. The tables are turned in this case and the best offence is a good defence!
With such an arising need, the market has more than a few spots for CTI analysts and other specialists who contribute to a safer and stronger digital environment. These specialists must be skilled beyond technology, and here we bring you some of the essential skills for a CTI specialist.
The process to gather, analyse and distribute CTI is usually similar in different organisations and has several steps. The objective is to monitor their own activity and study their data to find menaces or weaknesses before wrongdoers can exploit them.
Even if the different stages can change names or vary slightly, they start by defining the requirements for collecting information. They need to establish the CTI to proceed to its collection, raw, for now, as the next phase will be processing. In this stage, the raw data is organised and structured to find the potentially relevant data it contains. Once it is sorted, they analyse it to look for patterns or trends that provide a deeper understanding of the security status. The dissemination phase, as its name suggests, consists of sharing the relevant and actionable CTI with stakeholders and those involved with the organisation. The last step is the feedback received from them about how useful the information is and how much it can help the organisation.
During this process, specialists work with the different types of threat intelligence, which can be categorized into four types:
A high-level overview of the most likely to happen threats and other potential cyber-attacks, along with their consequences. This general analysis is made for a non-specialised audience to understand potential risks and consequences.
More specific information about attacker methodologies, techniques, procedures, and tools.
It helps organisations provide a more immediate response when facing a threat.
It consists of an in-depth analysis of threats from a technical perspective. At the same time, it provides the organisation with the tools and the technical procedure to follow in the occurrence of specific incidents.
Real-time information about ongoing cyber-attacks. It helps collect information from several sources to analyse it, catalogue it and identify the pattern in the event of similar future events.
The time of waiting for a cyberattack to happen to act is long gone and, through this prevention and analysis process of the four CTI types, organisations' safety is definitely stronger today.
CTI offers security information that allows organisations to strengthen their barriers and methods to protect themselves. However, contrary to the past, they can now use that information to actively find breaches, weaknesses, and patterns that make them vulnerable before an attack.
Due to the accelerated and unstoppable digital transformation taking place, the environment is rapidly changing and growing. Security has to keep up with the amount of data processed and the new menaces, something that will continue to happen in the future. Technology brings amazing methods to improve security but at the same time, it brings more sophisticated threats. Both sides evolve and race to overtake the other.
As it evolves it will demand more specific profiles, which will mainly divide into two tracks: cyber threat intelligence researchers and cyber threat intelligence analysts.
They work in a team as a whole and the process starts with the researchers. They keep track of APTs (Advanced Persistent Threats) and try to identify the motivations and techniques behind the attacks. As researchers, they will have to find current threats and be attentive to new models and menaces.
When researchers have a good overview of the situation, they provide analysts with feedback, which they will use by converting the vast amounts of data into actionable intelligence to safeguard the organisation’s digital assets. They analyse the feedback, dissect it and prioritise the information that is more relevant to the organisation’s sector and specific threats.
What CTI particularly provides within cybersecurity and through these professionals' work is a set of benefits that can change the game.
This discipline lets organisations ready themselves and look for possible menaces. Through constant gathering and analysis of data and the creation of countermeasures, security will be less prone to suffer beaches.
The amount of CTI provides enough information to create a custom solution for the organisation. Said solution will consider, not only the associated risks of its specific industry but also the unique needs of the company, based on analysed data and previous experiences.
The constant information gathering and analysis will identify any odd data caused by attacks, which will allow the company to react faster.
Regulations have become stricter which means that the sooner organisations update their security measures, the sooner they comply with the regulations, the less they will have to worry and rush in the future.
Providing a high level of security to clients and ensuring their data is protected can be more than enough for clients to choose your solution over someone else’s.
All these benefits and the need for specialists in CTI are reshaping the future of the digital environment and will continue to do so. A new landscape calls for a new player who has more than technical skills, but which ones will be the most important? Read on and find out!
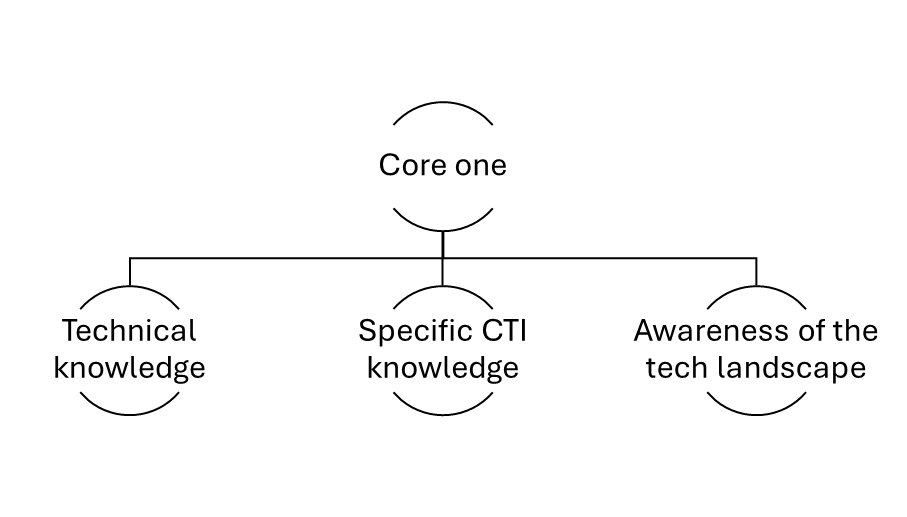
If you ever wanted to know whether working in CTI is for you, check how many of these skills you already have or you have to work on! And if you have to look for a CTI expert, these are some of the skills you need to look for in your candidates. These skills are divided into two cores: a technical and specialised one and a more human and subtle one.
In the first core, we have the technical skills which will be the foundation from which to build up. A CTI specialist must have wide technical knowledge that allows them to have a solid understanding of the digital landscape they have to move in. This environment involves coding, intrusion detection, prevention, incident response and any other tools and concepts around cybersecurity that can be proven useful.
Besides their knowledge of the digital environment, they must be familiar with the types of CTI they will be handling as well as with navigating the data and how to put it to good use. Mastering CTI also involves knowing about threat concepts, frameworks, actors and TTPs (tactics, techniques, and procedures).
The third part of this core would be having a general overview: of what is expected from the specific project, of the whole process in which CTI is involved, of the digital threat landscape… CTI is a discipline in which perspective is crucial and the wider it is, the better the result will be, and the better protected the organisation will be.
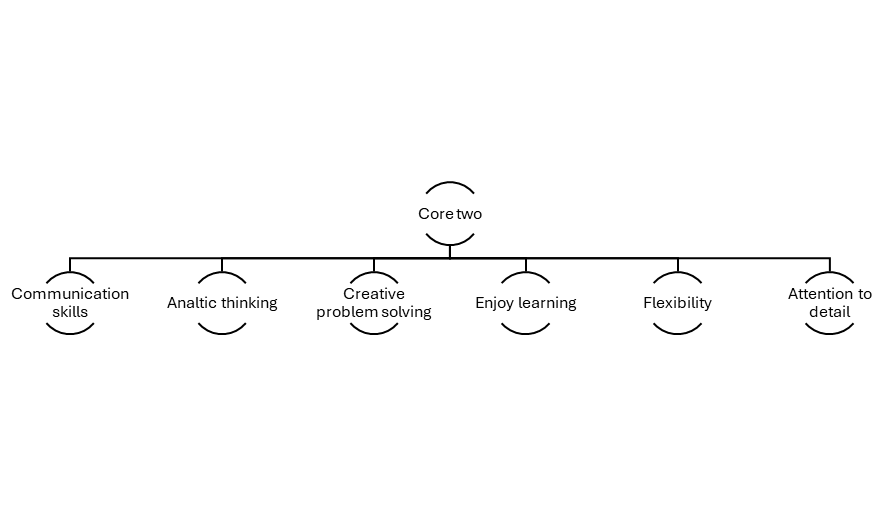
The second core has soft skills that complete the CTI expert profile. Even if they might seem less important than technical knowledge, they are the ones that complete the profile and make it perfect. Raw technical skill is of no use if the worker does not refine everything else surrounding it. Communication skills are key to successful teamwork, particularly in a field in which CTI specialists have to communicate complex technical information to both experts and non-experts. In a job with that many moving parts, it is beneficial to share information with all involved in order to obtain a bigger picture.
A communicative approach that integrates CTI into the whole company can also help enhance others of the necessary skills, analytic thinking and creative problem-solving. The wider the perspective is, the more resources and insights someone will have when facing data. Their mission is to look for menaces and weaknesses, which are easier to spot when you know the environment and the ongoing projects. Analytic thinking will help them find the problem while creative problem-solving will be the factor that differentiates them from other candidates. Being creative while solving a problem is especially advantageous in this field, as that is the way potential wrongdoers will think: you are covered. The less obvious your solutions are, the lower the probability of them trespassing.
In this discipline, threats and solutions evolve equally fast and that means that whoever working in the field must enjoy learning as well as new challenges. Working in tech means continuing to always learn, however, in CTI it is vital to be up-to-date with new trends, menaces and technologies that can be either useful or harmful.
If we have mentioned something throughout this article that is changes. The rapid evolution of the field along with the required responsiveness make flexibility a must for anyone working in the field. There is no real roadmap when analysing data unique to your organisation, this being the reason someone with great adaptability is perfect for this position.
Finally, a delicate and complex task like this calls for attention to detail. The quality and accuracy of the organisation’s security depend on the efficiency of its specialist and their ability to detect unusual data or vulnerable patterns.
Let us not forget that all of these skills will be improved through practical experience in the field. Any previous experience and additional knowledge in the tech field would be beneficial to carry out tasks in an optimal way.
CTI is the future of cybersecurity, and the future is already here. Trends and technological competitiveness allow companies to armour themselves against menaces before they even happen and to study the data they already have to improve their barriers. Changes like these prompted the creation of a new worker profile with a more complete set of skills and a more holistic approach.
If you consider you have these skills in your toolbox you are ready to hit the road! Visit our jobs page to find our chance to start building the future of cybersecurity.

Geoffrey (CEO) 'In concrete terms, entrepreneurship means going to the end of yourself and reach fulfillment thanks to a project. In a more...

Valencia is a seductive, charming, vibrant, and captivating city that...

Let’s be mysterious The name was created at the beginning of 2019, as it...